What is Bootsect.exe and How to Use It (Guide)
Typical Bootsect.exe mistakes
Bootsect.exe is one of the most common Windows error messages you’ll see. This article explains what it is and how to fix it.
How to fix errors with Bootsect.exe
Bootsect.exe errors are often caused by missing files or corrupted registry entries. In some cases, bootsect.exe errors occur due to malware infections. If you encounter bootsect.exe error messages, it might indicate that your system needs repair. You can use the Windows Installer Cleanup utility to fix bootsect.exe problems.
Download the appropriate version of the tool from Microsoft.
Run the program and follow the instructions to clean up the registry.
Reboot your computer once the process completes.
If you still experience bootsect.exe errors, try downloading and reinstalling the operating system.
How to Avoid Bootsect.exe on Your Computer
Bootsect.exe is a malicious program that is used to steal personal information such as login credentials and credit card numbers. This article explains how to protect your computer from being infected by Bootsect.exe.
The most common method of infection occurs when you download files from untrusted sources. When you open the file, it automatically installs Bootsect.exe without asking permission. If you do not delete the file immediately, you will end up downloading and installing malware onto your PC.
You must always check the source of downloaded files. If you cannot trust the sender, you should avoid opening the attachment. You can use anti-virus software to scan attachments for viruses before opening them. However, there are some types of malware that cannot be detected by antivirus programs. For example, Bootsect.exe uses encryption techniques to hide itself from detection. Therefore, you should manually remove the virus.
Steps To Remove Bootsect.exe Manually
1. In the Open box, type regedit.exe and press Enter.
2. Locate HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\ShellEx directory. Delete the value named ShellExePath.
3. Go to %SystemRoot%\system32\drivers\bootsect.sys folder. Right-click bootsect.sys and select Properties. Select the Compatibility tab, and then set the following settings:
What Characteristics Make Bootsect.exe a Virus or a Safe File?
Bootsect.exe is one of those files that you download without thinking twice about it. It seems like a harmless utility and it might even do what it says on the tin. However, there are some things that make us wonder whether it is actually legitimate. This article explains how you can tell if bootsect.exe is safe or malicious.
Check the File’s Location
The Task Manager is one of those tools that every computer user should know how to use. If you don’t know what it does, take some time to learn about it. Here are some tips to help you understand the basics.
If you’re having trouble locating a program, try searching your computer for the name of the app. For example, if you want to find out where Notepad is installed, type “notepad.” This method works best if you remember the exact name of the application.
You can also look inside the Program Files folder. In most cases, programs are stored there. However, sometimes developers place applications outside of the default location. Click the Browse button next to the Folders tab. Navigate to the Program Files directory and double-click the subfolder named Microsoft. Go into the All Users section and make sure the box labeled Show hidden files and folders is checked. Now go back to the main window and click OK. When you run the search again, you’ll see the missing program listed.
If you still can’t find the program, try looking in the Recycle Bin. Most operating systems keep a copy of deleted items here. To access the recycle bin, press the CTRL key while clicking on the Recycle Bin icon. Select the item(s) you’d like to restore and click Open.
Another way to find out where an application is installed is to use the Control Panel. On Windows 7, 8, and 10, open the Control Panel and navigate to the Appearance & Personalization category. Under the System heading, click on the Change PC Settings link. Next, choose Advanced system settings under the Performance heading. Finally, scroll down to Startup and Recovery and click on Restart now. A dialog box appears asking whether you want to restart the computer. Choose Yes and wait for the process to finish. After rebooting, log back in and open the Task Manager.
In Windows Vista, the steps are slightly different. First, open the Start Menu and select Control Panel. From there, choose Hardware and Sound. Then, choose Power Options. Scroll down to the bottom of the screen and click on Restart Now. Once the computer restarts, hold down the Shift key and hit Enter. Log back in and open the Control Panel. Repeat the same steps as above.
Finding A File’s Location
Open Task Manager and highlight the program name. Click on Properties. This opens the file’s properties dialog box. There you’ll find information about the file, including its path.
The location will vary depending on what type of operating system you’re running. For Windows 10, it’s usually %AppData%\Roaming\Microsoft\Windows\Recent\. On Linux systems, it’s usually ~/.local/share/recently-used/. On macOS, it’s ~/Library/Caches/com.apple.recent items list.
Verify your signature by doing so.
When you download something online, it usually arrives via email or some sort of attachment. If you receive a suspicious document, you’ll want to make sure it isn’t malware. One quick way to do that is to verify the digital signature. A digital signature is like a fingerprint – it identifies the person who signed the document.
The best way to verify a digital signature is to use a free tool called “Signature Check.” This utility scans documents for signatures and tells you whether they’re legitimate or not. You don’t even need to open the document; just run the scan.
If you find a questionable file, you can delete it immediately. Or you can move it into quarantine where it won’t harm your system, but you’ll still know about it.
Check the Size of the Bootsect.exe File
Bootsect.exe is a Windows executable file which is normally downloaded along with a virus infection. You can check the size of the file to see whether it matches the expected size. If you find out that the size does not match the expected one, you know that there is something wrong with the file.
You can use VirusTotal to scan the file for malware. You can download the free version of VirusTotal here.
How to Manually Uninstall Bootsect.exe from Your Computer
Bootsect.exe is an old variant of Win32/Brugit, a worm that infects Windows systems. This malware uses a technique called boot sector infection to hide itself within the operating system. Because it resides outside of the file system, it cannot be removed easily. However, there are several manual removal methods that you can use to rid yourself of this nasty piece of code.
Step 1: Run the Command at CMD
To run the cmd command, you must open the Windows Start menu. Press the windows start button. Then write the command ‘cmd’ into its textbox and click ok. This opens the command prompt.
Step 2: Locate the related DLL Files
In Step 1 we found out how to export Windows registry keys. Now it’s time to locate the required DLL files. To do this, open up Notepad and paste the following code into the document:
Save the file as RegExport.txt
Now you must run the program regedit.exe. This will allow us to access the Windows Registry Editor.
Open up the Windows Registry Editor. Navigate to HKEY_LOCATION_MACHINE\Software\Microsoft\Windows NT\. Open the WinLogon folder. You should see a few subfolders under here. One of those folders is named Shell. Open up the Shell folder. Inside there are several subfolders. Find the one called Userinit. Right click on the Userinit folder and select Export. Save the file somewhere safe.
Navigate to the location where you saved the file. Copy the entire contents of the file into Notepad. Paste the copied text into the same window. Save the file as shell.reg.
Run the command prompt again and type in the following commands:
Step 3: Reboot Your Computer
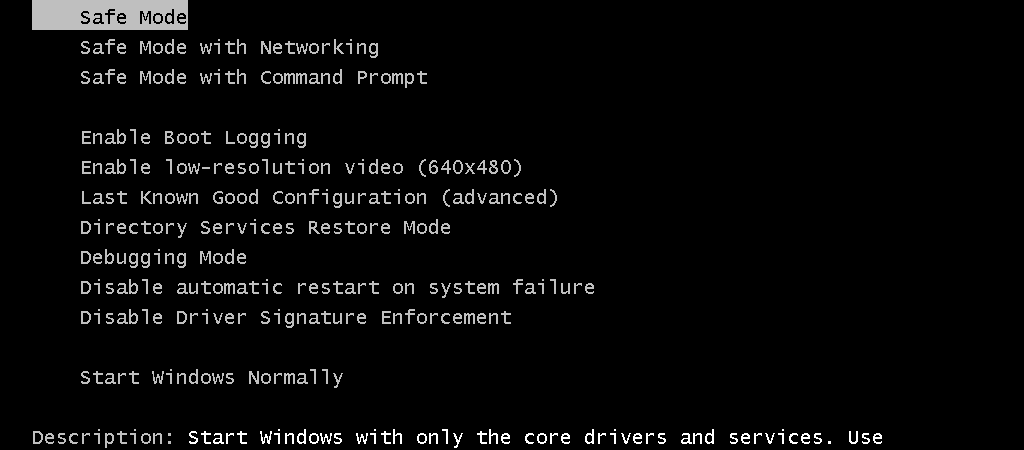
Reboot your computer. Select Restart Now and follow the instructions.
Click Choose what the power buttons do. Check Turn off automatically turn off my PC after X minutes. Then select When I shut down… choose Shut Down. Follow the instructions.
What Malware Removal Technique Should I Use, then?
Manual malware removal methods are dangerous. They could cause damage to your computer system. You must know how to use them properly. If you don’t, you might accidentally delete important files or make changes to your Windows registry that could render your PC useless.
Automatic malware removal tools are much safer. They scan your entire hard disk for malicious software and automatically remove it without causing any harm to your machine. These programs are usually safe to run because they’re designed to work within Windows’ built-in security features. However, some automatic tools require additional downloads and configuration steps.
There are several free automated malware removal tools available online. Some of them are easy to install; others require downloading and installing third-party applications. Most of them provide similar functionality and offer similar features. Here are a few popular ones:
Malwarebytes Anti-Malware Free – This tool offers real-time protection against viruses, spyware, rootkits, adware, browser hijackers and other types of malware. It works well for most PCs. The program includes a full range of scanner, anti-malware and cleaning functions.
Spybot Search & Destroy – Spybot Search & Destroy removes both known and unknown threats, including Trojans, keyloggers, worms, dialers and spyware. It scans and cleans infected files, processes, cookies, history, temporary Internet files, running apps, startup items and Windows Registry.
AdwCleaner – AdwCleaner removes unwanted advertisements, popups, toolbars and other junk installed on your PC. It can also clean up leftovers from previous virus infections.
ESET Nod32 Antivirus Plus – ESET NOD32 Antivirus Plus is one of the best antivirus solutions available today. It provides comprehensive protection against viruses, spy ware, trojans, worms, dialers, rogues, bots, root kits and other forms of malware. It protects your privacy and secures your data.

Tim Wiley was a tech writer for seven years at Recode. In that time, he covered everything from basic browser.js and URL parameters to XHRs, performance, malware, security, enterprise apps, social media, and Windows secrets. He also written about how to hack Signal in 2016 and how to resist, or possibly even conquer, the zero-day threat.