Process Explorer by SysInternals (now owned by Microsoft)
Process Explorer is a free task manager and system monitor for Microsoft Windows developed by SysInternals. The company was acquired by Microsoft and renamed into Windows Sysinternals. It provides the functionality of Windows Task Manager as well as a rich set of functions to collect information about the processes running in the user system. It can be used as a first step in troubleshooting software or system problems.
The Process Explorer can be used for troubleshooting. For example, it can be used to list or search for named resources held by a process or all processes. It can be used to find out what keeps a file open and prevents it from being used by another program. Another example: it can show the command lines used to launch a program, which can be used to distinguish between identical processes. Like the Task Manager, it can show a process that uses a processor to the maximum, but unlike the Task Manager, it can show which thread (along with the call stack) the processor uses – information is not even available in the debugger.
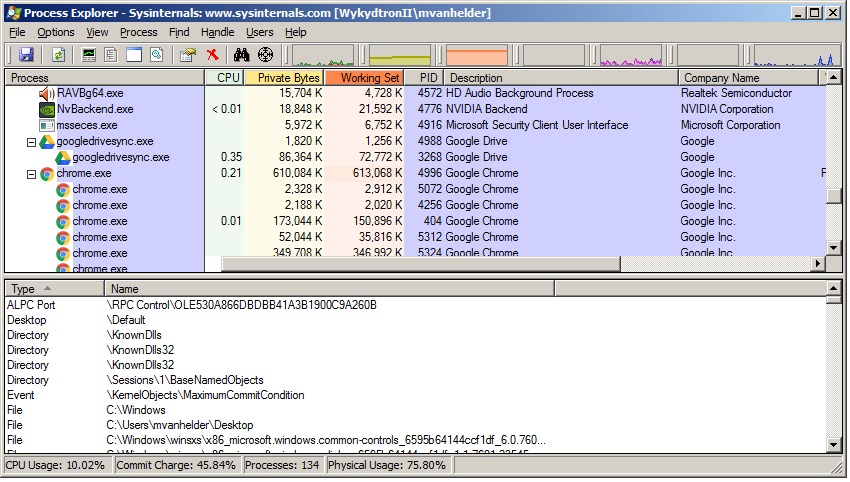
The Process Explorer display consists of two windowsills. The top window always displays a list of currently active processes, including the names of their own accounts, while the information displayed in the bottom window depends on the mode in which the Process Explorer is running: if it is in “handle” mode you will see the descriptors that the process selected in the top window has opened; if it is in “DLL” mode you will see the DLL and the memory files that the process has loaded. The process browser also has a powerful search function that will quickly tell you which processes have specific open descriptors or loaded DLLs.
Process Explorer’s unique capabilities make it useful for detecting DLL version issues or process leaks, as well as providing insight into how Windows and applications work.
Download
 Download Process Explorer (1.9 MB)
Download Process Explorer (1.9 MB)
Run now from Sysinternals Live.

Tim Wiley was a tech writer for seven years at Recode. In that time, he covered everything from basic browser.js and URL parameters to XHRs, performance, malware, security, enterprise apps, social media, and Windows secrets. He also written about how to hack Signal in 2016 and how to resist, or possibly even conquer, the zero-day threat.